Solving the Firewall and NAT Traversal Problems for SIP-based VoIP
As the demand of SIP continues to grow, companies continue to seek good solutions for the NAT-T (Network Address Translation - Traversal). The issue of NAT traversal is still an obstacle to widespread adoption of SIP and the reality of converged communications. Many companies today are looking for the right solution to bring the benefits of such collaboration into their network – and to do so while maintaining security and control.
What is NAT Traversal?
The purpose of a Network Address Translation (NAT) firewall for businesses is to provide the translation between a single public IP address on the WAN and multiple private IP addresses for all of the workstations, servers and other IP equipment within the LAN.

The router running NAT should never advertise the LAN network addresses to the WAN network backbone. Only the networks with global addresses may be known outside the router. However, global information that NAT receives from the border router can be advertised in the LAN network the usual way. Typical or traditional firewalls apply NAT to the TCP/IP protocol at the transport and network layers.
Get in touch

What is the problem with SIP, VOIP & NAT?
SIP-based communication does not reach users on the local area network (LAN) behind firewalls and Network Address Translation (NAT) routers automatically. Firewalls are designed to prevent inbound unknown communications, and NAT stops users on a LAN from being addressed. Firewalls are almost always combined with NAT and typically still do not support the SIP protocol properly.
This issue of SIP traffic not traversing the enterprise firewall or NAT is critical to any SIP implementation, including VoIP.
Since the addressing and routing of SIP is done at the application layer, the biggest problem the SIP protocol still has is the disconnect between the IPv4 addressing and routing at the application layer versus the IPv4 addressing and routing at the transport and network layers. Network Address Translation (NAT) occurs at the transport and network layers, and thus the challenge.
In order for SIP to work effectively, the NAT issue must be resolved, and that is where the Session Border Element such as the SIP Firewalls and SIParators offered by Ingate, are very important for enabling SIP services to an enterprise network.
What is the solution for the SIP NAT issue?
There are numbers of available methods for firewall traversal. Each has its own benefits; many have significant drawbacks. These drawbacks impact security.
The choice of method for traversing firewalls/NATs determines the amount of control and security you maintain of your network. Is your security best left to your firewall administrator? The individual user? Your service provider? Also, does the solution need to work with all operators, or only one specifically?
How SIP-compliant does it really need to be? Will SIP interoperability issues affect security?
The answers can help determine which method of firewall/NAT traversal is right for your network.
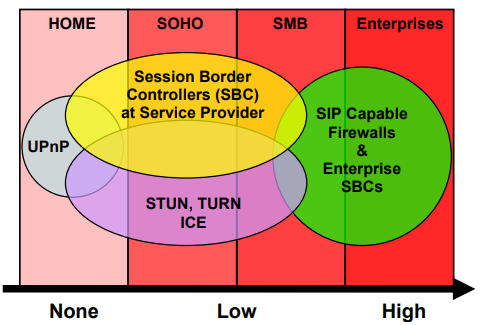
SIP-capable Firewalls or enterprise SBC – The firewall administrator is in control
This is a long-term solution where the problem is solved where it occurs, at the firewall or in tandem with an existing firewall using an enterprise session border controller. When deployed at the enterprise edge the SBC offers the same security and control as it does for the service provider’s core network. The enterprise SBC typically has a built-in SIP proxy and/or back-to-back user agent (B2BUA) functionality to give unparalleled flexibility in real-life enterprise deployments.
Most vendors of SBCs for service providers have products that can be deployed at the enterprise and then there are companies like Ingate Systems that have developed products for the enterprise market from the very beginning. Ingate’s SIParator™ is such an enterprise SBC.
For an enterprise, there are special security and functional requirements that make the SIP-capable firewall or enterprise SBC the solution of choice. First, it is the only solution that allows the firewall to maintain control of what is traversed between the LAN and the outside world. In addition, it is becoming more and more common to have a SIP server on the LAN. In fact, all SIP-based IP PBXs are SIP servers. In order for these SIP servers to communicate over IP with the outside world, the firewall simply must be SIP-enabled. As many IP-PBXs have done their own SIP-extensions outside the SIP standard it is very important that the firewall or enterprise SBC be adapted to support these extensions.
Due to the complexity of real-life installations, it is highly recommended to deploy specialized SIP-enabling devices such as SIP-proxy firewalls even in the SOHO and SMB markets, even if it might not be motivated from a security policy perspective.
Learn all about how Ingate is
Solving the Firewall/NAT Traversal Issue of SIP in this pdf.
Benefits of Ingate Session Border Controllers
• Market-proven E-SBC products delivered by a reputable supplier that's easy to work with
• Competitive session pricing and positive ROI with attractive margins to surpass our competition
• Easy to connect SIP trunks to PBXs, Unified Communications (UC) solutions and call centers (recent case study).
• Access to Ingate pre-sales training, free of charge
• Direct support for technical recommendations
• Support for marketing, sales and implementation
• FREE SBC Software for Trials
• Interoperable E-SBC with all IP-PBXs and ITSPs
The Ingate SIParator™ is a powerful, flexible and cost-effective Enterprise Session Border Controller (E-SBC) for SIP connectivity, security and interoperability, such as connecting PBXs and Unified Communications (UC) solutions to SIP trunking service providers. Read more about our hardware and software solutions.
For any questions, free trials or offers, please contact us today.




